To print this article, all you need is to be registered or login on Mondaq.com.
Executive Summary
Our Privacy, Cyber & Data Strategy and Privacy &
Cybersecurity Litigation teams examine the New York Department of
Financial Services’ finalized Second Amendment to its
Cybersecurity Regulation.
- The regulations expand on when cybersecurity events require
notice to NYDFS – including after deployment of ransomware
and extortion payments - Covered entities must expand their use of multi-factor
authentication, maintain an asset inventory, and operationalize
policies through developed procedures - Senior officers must have sufficient knowledge to oversee the
company’s cybersecurity program, and both the CISO and highest
ranking executive must certify compliance annually
On November 1, 2023, the New York Department of Financial
Services (NYDFS) published the finalized Second Amendment to its Cybersecurity
Regulation (23 NYCRR Part 500), which includes a number of
significant and, for many covered entities, onerous changes to its
original regulation. The finalized Second Amendment is much like
the June 2023 proposed draft (which made certain
revisions to the November 2022 draft). Covered entities should
take note of these now-final changes that will require covered
entities to review and revamp major components of their
cybersecurity programs, policies, procedures, and controls to
ensure they are in compliance. This is particularly important as
the NYDFS continues to take on an active enforcement role following
cyber events, marking itself as a leading cyber regulator in the
United States.
Covered entities must notify the NYDFS of certain cybersecurity
incidents, including providing notice within: (1) 72 hours after
determining a cybersecurity event resulting in the “deployment
of ransomware within a material part of the covered entity’s
information system” occurred; and (2) 24 hours of making an
extortion payment in connection with a cybersecurity event.
Covered entities must implement additional cybersecurity
controls, including expanding their use of multi-factor
authentication and maintaining a comprehensive asset inventory.
Covered entities are also required to maintain additional (or more
prescriptive) cybersecurity policies and procedures, including
ensuring that their incident response plans address specific
delineated issues (outlined in the Second Amendment) and
maintaining business continuity and disaster recovery plan
requirements (both of which must be tested annually).
The most senior levels of the covered entity (senior governing
body) must have sufficient knowledge to oversee the cybersecurity
program. Additionally, the highest-ranking executive and the CISO
are required to sign the covered entity’s annual certification
of material compliance.
A material failure (which could be a single act) to comply with
any portion of the Cybersecurity Regulation for a 24-hour period is
considered a violation.
The Second Amendment became effective on November 1, 2023, and
covered entities generally have 180 days to come into compliance
with the new requirements. There are certain requirements, however,
that will be phased in over the next two years. We have outlined
the material changes and the effective dates below.
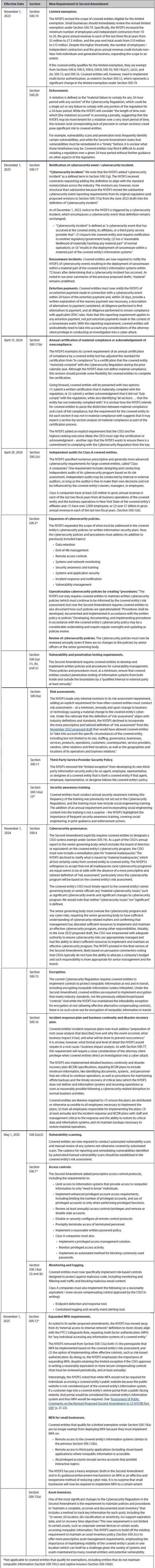
The NYDFS is providing a number of resources for covered
entities, including a helpful visual overview of the implementation
timeline for covered entities, Class A companies, and small businesses (NYDFS-licensed individual
producers, mortgage loan originators, and other businesses that
qualify for exemptions under Sections 500.19 (a), (c), and (d)).
The NYDFS is also hosting a series of webinars to provide an
overview of the Second Amendment; individuals can register for the
webinars on the NYDFS’s website.
The content of this article is intended to provide a general
guide to the subject matter. Specialist advice should be sought
about your specific circumstances.
POPULAR ARTICLES ON: Technology from United States















